Most Common Cyber Attacks: Real-World Examples, Impact, and How Organizations Respond
April 2026 Cyber security attacks

In today's hyper-connected digital landscape, cyber-attacks are no longer rare incidents, they are daily threats impacting organizations of all sizes. From financial losses to reputational damage, the consequences can be severe and long-lasting.
Understanding the most common types of cyber-attacks, along with real-world examples and mitigation strategies, is essential for building a resilient cybersecurity posture.
1. Phishing Attacks
What is Phishing?
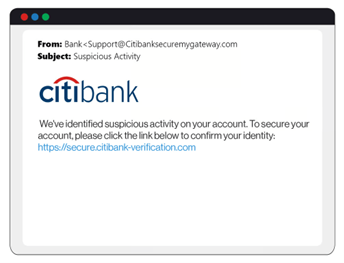
Phishing is a social engineering attack where attackers trick individuals into revealing sensitive information such as passwords, credit card details, or login credentials. The attackers impersonate trusted entities like banks, internet service providers, govt. institutions etc. They use email, SMS, phone calls, or social media to contact the victims.
Phishing attacks typically follow a cycle: attackers plan and gather target information, craft deceptive messages, send them at scale or to specific individuals, and harvest credentials or deploy malware once victims click malicious links or attachments. These attacks exploit human psychology rather than technical vulnerabilities, making them one of the most effective and widespread threats today.
Types of Phishing Attacks
- Email Phishing: Attackers send mass emails impersonating banks, services, or colleagues. The emails may ask for sensitive data or have links to deceptive looking websites where you need to input your login credentials.
- Spear Phishing: These are highly targeted attacks using personal/professional details. An attacker may get your details from social media and use it to contact you and trick you into revealing sensitive information.
- Whaling: C-level executives in companies have access to company data and accounts. Attackers may specifically target these individuals to gain access to this information.
- Smishing: Instead of using emails attackers may use SMS/text messages. These messages will have malicious links which will lead to deceptive websites where the victim may enter their credentials
- Vishing: This refers to voice phishing over phone calls. Attackers may call saying that they are from a trusted institution like a bank. They can use excuses like KYC updation to gather information like credit card details.
- Quishing: QR Codes are becoming ubiquitous. We generally scan them without much thought. In QR code-based phishing the attackers redirect the code to malicious sites
- Angler Phishing: The victims can be contacted by fake social media customer support accounts and tricked into giving details like login credentials.
Real-World Examples
1. Target Data Breach (2013)
One of the most famous phishing-related attacks involved retail giant Target. Attackers gained access through a phishing email sent to a third-party vendor. Around 40 million credit/debit card records of customers were compromised.
2. Google and Facebook Fack Invoice Scam (2013 - 2015)
An attacker sent Google and Facebook fake invoices impersonating a genuine supplier. The companies reportedly paid over $100 million over a two-year period to the scammer.
How to Prevent Phishing Attacks
For Individuals
- Enable Multi-Factor Authentication (MFA) MFA adds a second layer of protection beyond just passwords. The attackers will need access to One Time Passwords to log in to the account.
- Verify sender addresses Attackers create fake websites that look deceptively similar to real websites. Before clicking a link, please check for subtle misspellings or suspicious domains
- Don't click suspicious links Hover to preview URLs before clicking. This will reveal the actual redirect link which can be checked against real links of banks or other institutions.
- Keep software updated Auto-update OS, browsers, and security tools. These tools usually have anti-phishing protection. They block suspicious websites preventing your data from being leaked.
- Use password managers Password managers are great to protect your credentials. They create hard to guess passwords. They also prevent auto-fill of passwords on fake sites.
For Organizations
- Security awareness training Organizations should conduct regular phishing simulations and education for their employees. They should be encouraged to report any suspicious emails to the IT department.
- Email authentication protocols They can Implement email authentication protocols like SPF, DKIM, and DMARC on their servers. This will block any suspicious emails from reaching the inbox of the employees.
- Anti-phishing tools Organizations should deploy anti-phishing tools like firewalls, email filters, and endpoint protection.
- Verify financial requests The finance departments of the organizations should implement a multi-step approval process for wire transfers. No invoices should be processed without cross verification and approval. In case of any changes in the account details, the same should be independently verified with the vendor before processing the invoices.
2. Ransomware Attacks
What is Ransomware?
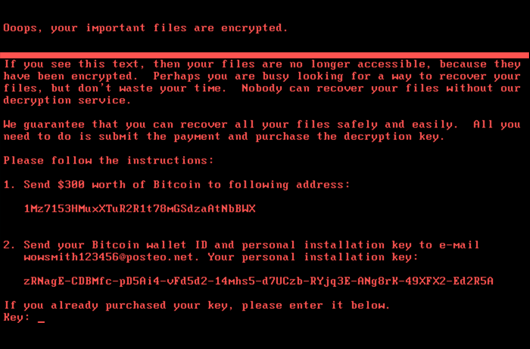
Ransomware is a type of malware that encrypts an organization’s data and demands payment (usually in cryptocurrency)
to restore access. The attackers may also steal sensitive data before
encryption and threaten to leak it publicly if the ransom isn't paid, a tactic known as "double extortion".
Ransomware attacks typically follow a staged process:
- Initial Access - Via phishing emails, exploited vulnerabilities, or compromised remote desktop protocols (RDP)
- Escalation - Attackers gain deeper system control using remote access tools
- Scanning - The malware maps the network to identify high-value targets
- Encryption - Critical files and databases are locked using strong cryptography
- Ransom Demand - A note appears with payment instructions and deadlines
Real-World Examples:
1. WannaCry Attack (2017)
The WannaCry ransomware attack affected over 200,000 systems across 150 countries, including the UK’s National Health Service (NHS). It caused approximately $4 Billion in damage globally.
2. AIIMS Ransomware Attack (2022)
AIIMS, Delhi was hit by a ransomware attack which targeted the hospital’s sensitive data, including patient records, research data, and administrative information. The attackers demanded $25 Million to release the data.
How to counter ransomware attacks
- Organizations should conduct regular patch management. Operating systems and software regularly update their security by releasing patches. Implementing these patches can help prevent ransomware attacks
- Improved backup and recovery systems are key to protect yourself from ransomware attacks. If your data is regularly backed up, you will be less susceptible to the ransomware as you will be able to switch to an offsite backed up data.
- Network isolation is paramount to fight ransomware attacks. If your network is segmented it limits the spread of the attack from one node to another.
- An organization should have a robust incident response plan. In case of an attack they should be able to switch to an offsite system to ensure continuity of operations. They should regularly test their offsite data backup and recovery processes.
3. Man-in-the-Middle (MITM) Attacks
What is a MITM Attack?
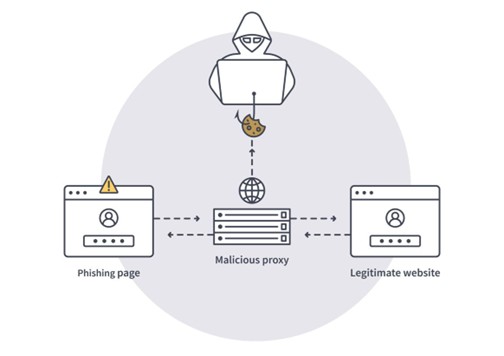
In a Man-in-the-Middle attack, the attacker secretly intercepts and possibly alters communication between two parties without their knowledge. These attacks exploit unsecured networks, weak encryption, or trust relationships, making them a persistent threat in online banking, email, and web browsing.
MITM attacks typically unfold in three phases. First, attackers gain interception position through techniques like ARP spoofing (faking network addresses), DNS poisoning (redirecting traffic), or creating rogue Wi-Fi hotspots. They then decrypt or access the traffic often by stripping HTTPS encryption or using malware, and finally exploit the data for credential theft, session hijacking, or transaction manipulation.
Real-World Examples:
1. Equifax Mobile App Vulnerability (2017)
Equifax had a flaw in its mobile app that made it vulnerable to MITM attacks, allowing attackers to intercept sensitive data. The attackers were able to access sensitive customer information like credit card details of 147 million customers.
2. Evil Twin on Flight (2024)
Attackers set up a fake in-flight Wi-Fi hotspot. When passengers connected to the same their credentials were stolen mid-flight. Similar rogue hotspots on public Wi-Fi networks like cafes or malls can be used to get customer data.
Corrective Measures to Counter MITM attacks
- Avoid public Wi-Fi for sensitive tasks. If you are logging on to the internet on a public Wi-Fi network, like on a café, hotel or airplane, it is possible that it is a rogue network designed to access your credentials. You should use VPNs with strong encryption while accessing such networks.
- Always verify HTTPS (padlock icon) and use HSTS-enabled sites. These sites are more secure than HTTP sites and your data is less susceptible to MITM attacks.
- Implement certificate pinning and check for unexpected browser warnings. Websites should implement mutual TLS for server-client authentication. MITM attacks thrive on unencrypted channels and user trust, but layered defenses like end-to-end encryption (e.g., TLS 1.3) and vigilant habits make them far less effective.
Ransomware attacks typically follow a staged process:
- Initial Access - Via phishing emails, exploited vulnerabilities, or compromised remote desktop protocols (RDP)
- Escalation - Attackers gain deeper system control using remote access tools
- Scanning - The malware maps the network to identify high-value targets
- Encryption - Critical files and databases are locked using strong cryptography
- Ransom Demand - A note appears with payment instructions and deadlines
4. Distributed Denial-of-Service (DDoS) Attacks
What is a DDoS Attack?
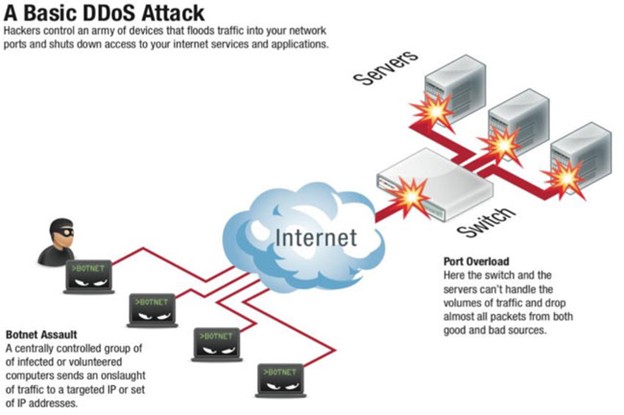
A DDoS attack floods a server, network, or website with excessive traffic, causing it to crash or become unavailable. DDoS attacks overwhelm online services with fake traffic from multiple sources. These distributed denial-of-service incidents exploit botnets of compromised devices to flood targets like websites or networks. Attackers first build a botnet by infecting thousands of devices (IoT gadgets, PCs, servers) with malware via phishing or exploits. They then coordinate a massive flood of requests, such as HTTP floods, SYN floods, or UDP amplification, to exhaust bandwidth, CPU, or memory, causing slowdowns or crashes.
Real-World Examples:
1. Dyn DNS Attack (2016)
A massive DDoS attack on Dyn, a DNS provider, disrupted major websites like Twitter, Netflix, and Reddit. It caused major internet outages across the US and Europe. The services were down for hours resulting in loss of revenue for affected companies.
2. Evil Twin on Flight (2020)
Amazon Web Services was attacked in 2020. At its peak AWS was getting requests up to 2.3 Tbps. It was a record volumetric attack using CLDAP amplification
Corrective Measures against DDOS attacks
- Deployment of DDoS mitigation services with always on protection.
- Traffic filtering and rate limiting. Set thresholds on SYN, UDP, ICMP floods; drop excess packets early.
- Use of Content Delivery Networks (CDNs) like Cloudflare or Akamai for traffic scrubbing
5. SQL Injection Attacks
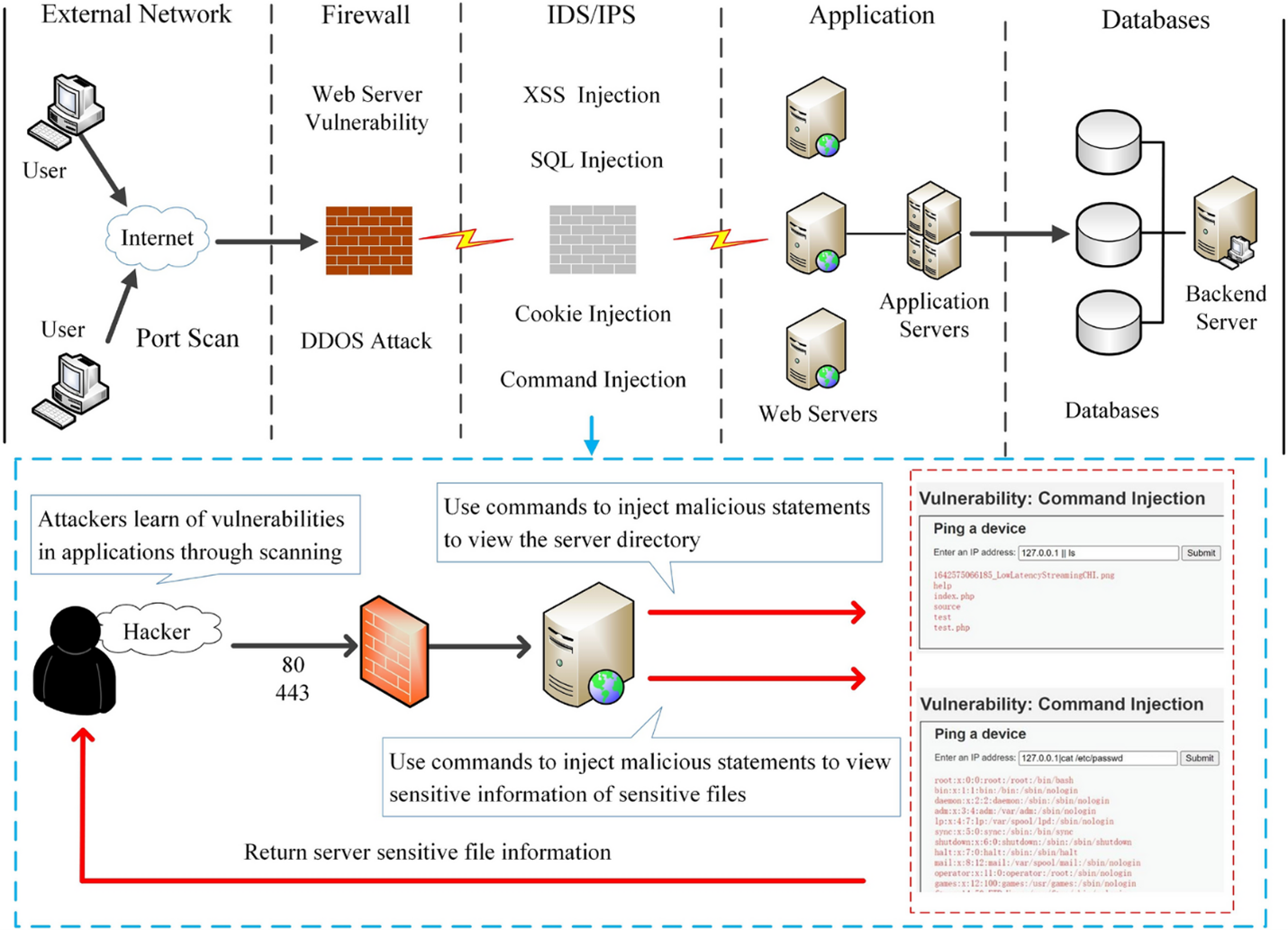
What is SQL Injection?
SQL injection (SQLi) attacks exploit vulnerabilities in web applications by injecting malicious SQL code into input fields, allowing attackers to manipulate database queries. These attacks remain one of the OWASP Top 10 threats, potentially exposing sensitive data, bypassing authentication, or executing system commands.
Real-World Examples:
1. Yahoo Data Breach (2012-2013)
A massive DDoS attack on Dyn, a DNS provider, disrupted major websites like Twitter, Netflix, and Reddit. It caused major internet outages across the US and Europe. The services were down for hours resulting in loss of revenue for affected companies.
2. Evil Twin on Flight (2011)
In this massive data breach 77 million user accounts were exposed. The attackers gained access to usernames and passwords.
Prevention and Mitigation
- SQL injection is completely preventable using prepared statements with parameterized queries. This defense is used by all modern frameworks. Never trust user input; always validate, sanitize, and use proper database APIs. Regular security testing catches what code reviews miss.
- Web Application Firewalls (WAFs) like Imperva and ModSecurity can be used to detect SQLi patterns
6.Credential Stuffing Attacks
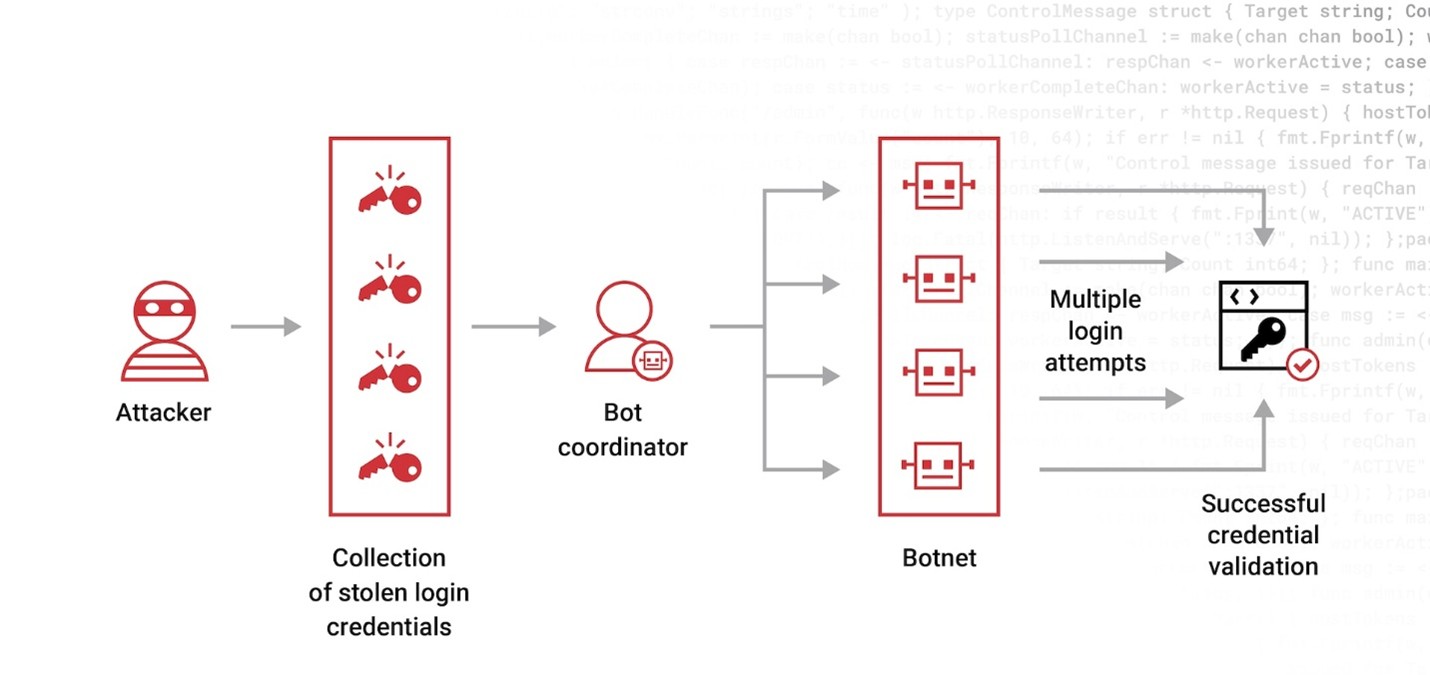
What is Credential Stuffing?
This attack uses stolen usernames and passwords (often from previous breaches) to gain unauthorized access to user accounts across different websites, exploiting users who reuse credentials. Attackers automate millions of login attempts with bots.
Attackers buy breach dumps from dark web markets. This gives them access to millions of credentials. They use botnet automation to deploy headless browsers mimicking human behavior across proxies. They use mass login attempts to test credentials across multiple websites. If any credentials work they can commit fraud or datatheft.
Real-World Examples:
1. Zoom Attacks (2020)
Thousands of Zoom accounts were compromised due to credential stuffing using reused passwords. The attackers gained unauthorized access to meetings leading to privacy and data breaches.
2. LinkedIn Breach (2012)
The attackers targeted Enterprise SAAD sites using the data breached from LinkedIn. 117 million corporate emails were compromised in that breach.
Corrective Measures Against Credential Stuffing
- The users must improve their password hygiene. It is inadvisable to use the same password across multiple sites. This way even if the password for one site is compromised in a data breach the other accounts are safe. The users can use password managers to create unique passwords for all accounts
- Multi Factor Authentication (MFA) is the best defense against credential stuffing. Even if your data has been compromised, the attackers cant access your account without the one time passwords.
Conclusion
No organization is immune to cyber threats. However, learning from real-world attacks provides valuable insights into strengthening defenses and reducing risk. A proactive approach combining technology, processes, and people is the key to staying ahead in the cybersecurity landscape.
Cyber Security courses from Cyber Skillshala help you understand the tools and techniques that you can use to stop these cyber attacks. Companies across industries are recruiting cyber security professionals in various roles so that they can protect their data from these attacks. A certification from Cyber Skillshala will help you get into these roles. Contact us to know more.